Cache Recitation
In the website fingerprinting lab, we learned how to use coarse grained microarchitectural measurements to infer system behavior. Starting in the cache attacks lab, we will be performing a much more fine grained analysis of cache contents to learn exact secrets using techniques like prime+probe and flush+reload.
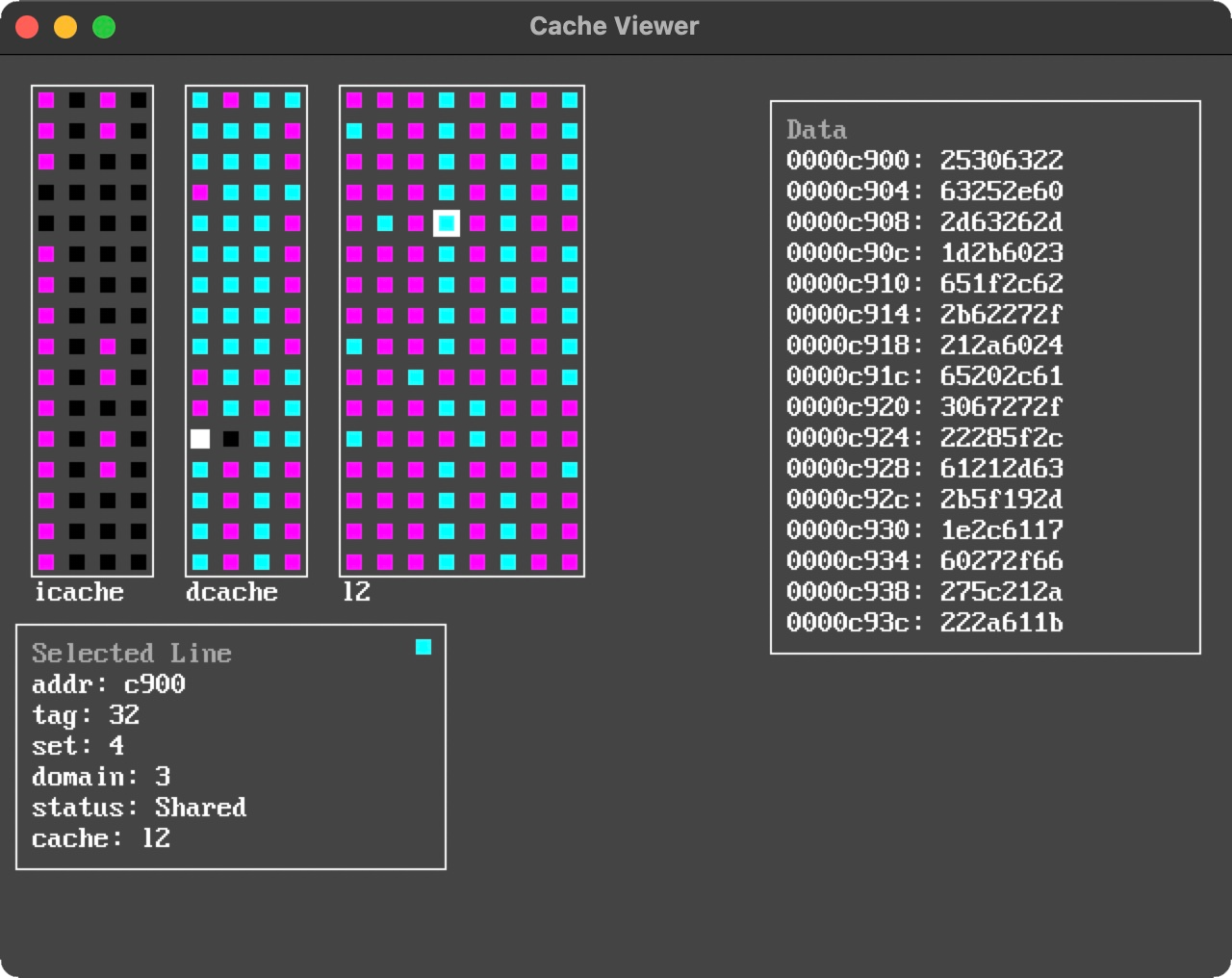
In today’s recitation, we are going to start by demystifying the website fingerprinting attack to better understand why the attack works when memory accesses are removed. Next, we will learn how CPU caches are implemented on Unicorn, the server you will be implementing your attacks on. Finally, we are going to learn how prime+probe works at a high level using a microarchitectural attack simulator.
- We will be going over the Bigger Fish paper to learn more about the website fingerprinting attack.
- Next, we will be learning about the Unicorn cache organization.
- Finally, we will be using the simulator from Modeling Microarchitectural Side Channel Attacks for Fun and Profit. Specifically we will be going over Sections 2.1, 2.2, 2.4, 2.5, and 6.2.